Encrypt sensitive files
Do you have files that you do not want others to see? Perhaps you keep your tax returns archived on your hard drive. Or your employee's files at work. Using a very simple, free program you can protect those files from others accessing them using TrueCrypt. Version 5.1a was released March 17, 2008, so you know this isn't some beta software you're running.
From the TrueCrypt website, here are its main features:
 Being tax season, if you share your computer with others or share files on your computer, it's time to get a little more serious about protecting your critical files -- whether you're using Windows, Mac or Linux, give TrueCrypt a try.
Being tax season, if you share your computer with others or share files on your computer, it's time to get a little more serious about protecting your critical files -- whether you're using Windows, Mac or Linux, give TrueCrypt a try.
From the TrueCrypt website, here are its main features:
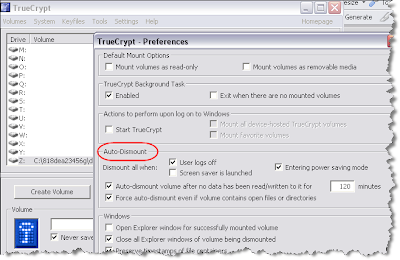
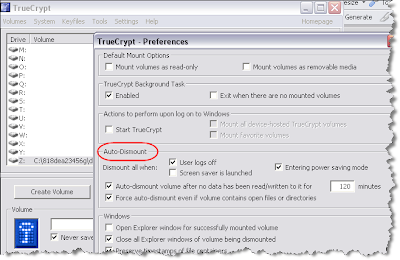
TrueCrypt is easy to use too. After installation, follow the Wizard; there is even a beginner's tutorial on the TrueCrypt website that walks you through the Wizard. Once you have created your TrueCrypt repository, you can treat it like any other drive to read and write files. And then TrueCrypt has various settings to help protect yourself so you never leave an encrypted repository open for other users of your system. You can even assign hot-keys to mount or unmount your encrypted drive(s).
- Creates a virtual encrypted disk within a file and mounts it as a real disk.
- Encrypts an entire partition or storage device such as USB flash drive or hard drive.
- Encrypts a partition or drive where Windows is installed (pre-boot authentication).
- Encryption is automatic, real-time (on-the-fly) and transparent.
- Provides two levels of plausible deniability, in case an adversary forces you to reveal the password:
- 1) Hidden volume.
- 2) No TrueCrypt volume can be identified (volumes cannot be distinguished from random data).
- Encryption algorithms: AES-256, Serpent, and Twofish. Mode of operation: XTS.
 Being tax season, if you share your computer with others or share files on your computer, it's time to get a little more serious about protecting your critical files -- whether you're using Windows, Mac or Linux, give TrueCrypt a try.
Being tax season, if you share your computer with others or share files on your computer, it's time to get a little more serious about protecting your critical files -- whether you're using Windows, Mac or Linux, give TrueCrypt a try.

Comments